company
About SnapAttack.
The Problem: In today’s threat landscape, the journey to “proactive cybersecurity” is riddled with barriers.
there's a people problem
Because between the talent shortage and high turnover in security operations, finding the right people is hard enough. And it doesn’t help when teams are playing a constant game of “gotcha” instead of working towards the same objectives.
there's a data problem
Because if your data isn’t accurate, adequate, centralized, or actionable, it is next to impossible to measure or improve your security coverage – let alone have any meaningful confidence in it.
there's a tools problem
Because yes, there may be an abundance of tools that claim to solve problems, but differing query languages and clunky integrations often create more problems than solutions.
These challenges, coupled with rapid digital transformation, the rise of cryptocurrency, and the mobilization of cybercriminal enterprises have created a perfect storm for companies and public sectors alike.
We may not want to admit it, but bad actors got something right. They’ve learned from each other. They’ve simplified their processes and built entire enterprises on the dark web. And, they’ve removed barriers to scale every step of the way.
Meanwhile, an industry-wide duplication of effort exists around building detections. Everyone is so focused on protecting their reputation that they’re missing out on a huge collaboration opportunity.
That’s why we created SnapAttack.
our story
SnapAttack was built to attack hackers with a hacker mindset.

SnapAttack was born out of Booz Allen’s Dark Labs – an incubator housed within one of the largest cybersecurity consultancies in the world. The resources of BAH enabled SnapAttack to mobilize an elite team to examine the problems facing public sectors, enterprises, and cybersecurity companies. Our goal was simple: come up with an innovative, practical solution – one that could leverage our experience with commercial and nation-state-level cyber operations to help organizations stop a cyberattack before it occurs.
And that’s what we did.
But make no mistake, SnapAttack has carved out its own path since its inception. In 2021, SnapAttack established itself as a standalone company. Since then, we’ve been hard at work, rapidly evolving the platform, enabling proactive threat hunting, removing barriers to detection as code, and advocating for purple teaming – all in one, integrated platform.
Proud of where we came from. Excited for where we’re going.
before + after snapattack
vulnerability exposure
Before SnapAttack: 7 days
After SnapAttack: 1 day
detection testing + deployment
Before SnapAttack: 12 hours
After SnapAttack: 1 hour
threat intel curation
Before SnapAttack: 75 hrs / week
After SnapAttack: 20 hrs / week
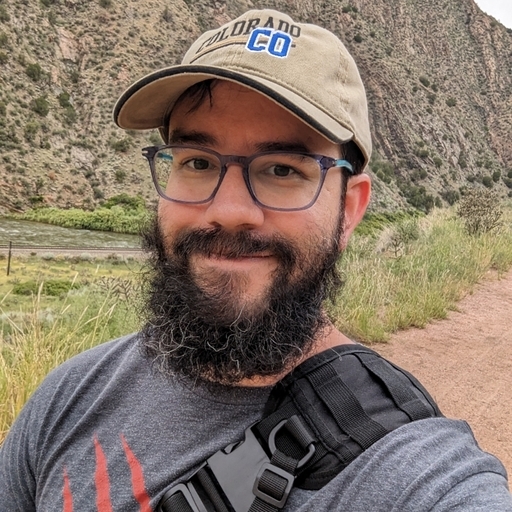
leadership team + board of advisors
Built BY security leaders, threat hunters, and red teamers FOR security leaders, threat hunters, and red teamers.
investors
Individual

Clayton Barlow-Wilcox
Chief Operating Officer, SnapAttack
careers

Matt Bowen
Frontend Engineer

Jordan Camba
Sr. Solutions Architect
Paul Carrillo
Sr. Security Engineer

Jacob Delgado
Sr. Backend Engineer
Michael Drinkwater
Sr. Backend Engineer

Tessa Georgen
Content Automation

Kevin Johnson
Frontend Engineer

Justin Kaldenbach
Sr. Full Stack Engineer

Russell Schaffer
Director of IT

Raven Tait
Threat Researcher

Claire Robertson
Customer Success Manager

AJ King
Director of Threat Research

Jonathan Woodell
Backend Engineer

Beesly
Chief Morale Officer
why snapattack?
Built to enable the good guys to do good work with dozens of direct integrations.
DOWNLOAD: SNAPATTACK INTEGRATIONS
SnapAttack was built to power not just one tool, but to help you get the most out of any security tool. Legacy tooling has driven cybersecurity teams into a cycle of constantly buying, configuring, and managing tool after tool, new ones hitting the market every day as existing ones become obsolete. Explore the platform’s 30+ direct integrations to understand what SnapAttack can do for you.